CLounge Value
All-in-One Service
Provides all the necessary services for business management, e-approval, time and attendance management, etc.
Supported by AWS
Utilized the storage security and backup features of the cloud platform to enhance security backup capabilities.
Add-On Service
Customize your CLounge with some of our additional services that will make your job easier.
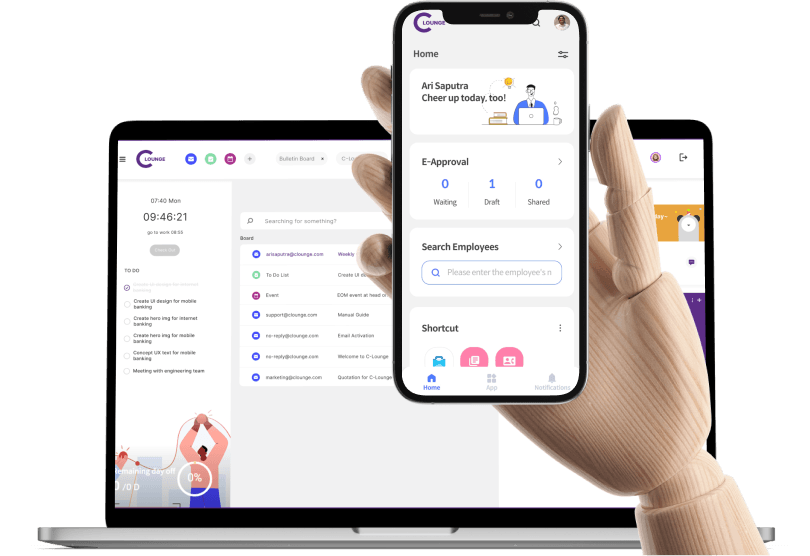
Captivated UI/UX Design
Our UI/UX design captures and reflects the latest trends in design, ensuring an engaging and modern user experience.
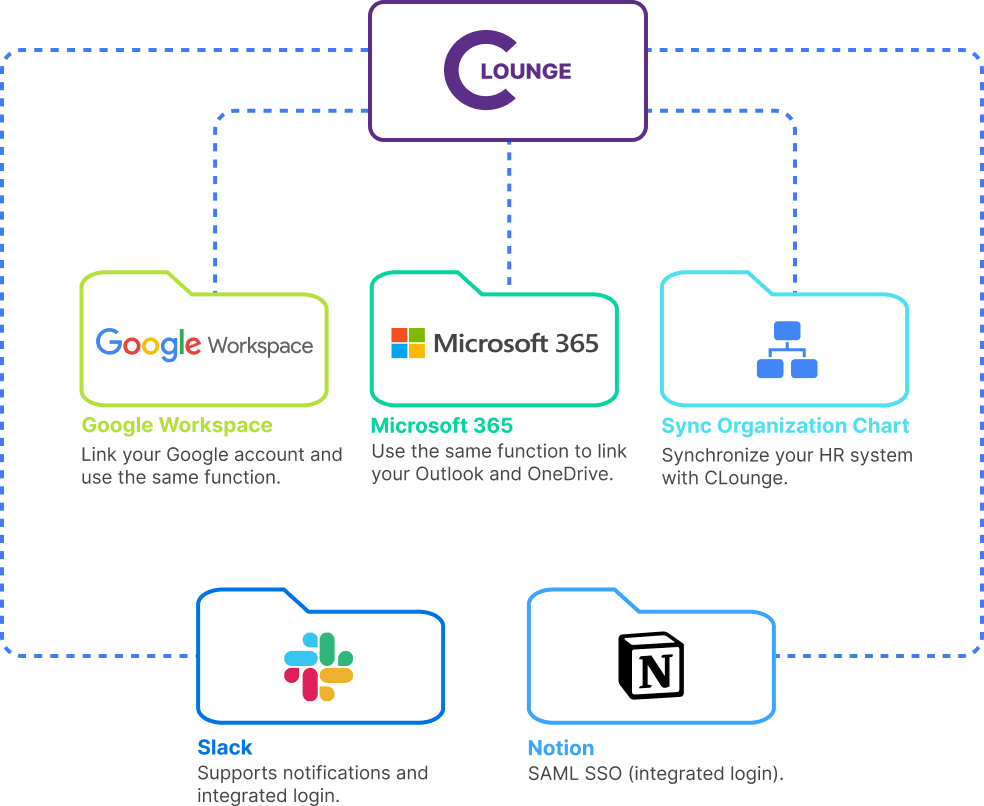
Workspace Integration
CLounge can support the optimal environment for Google or Microsoft users.
Integrated SaaS
Seamless business access through SSO authentication, connect and integrate all services for a great user experience
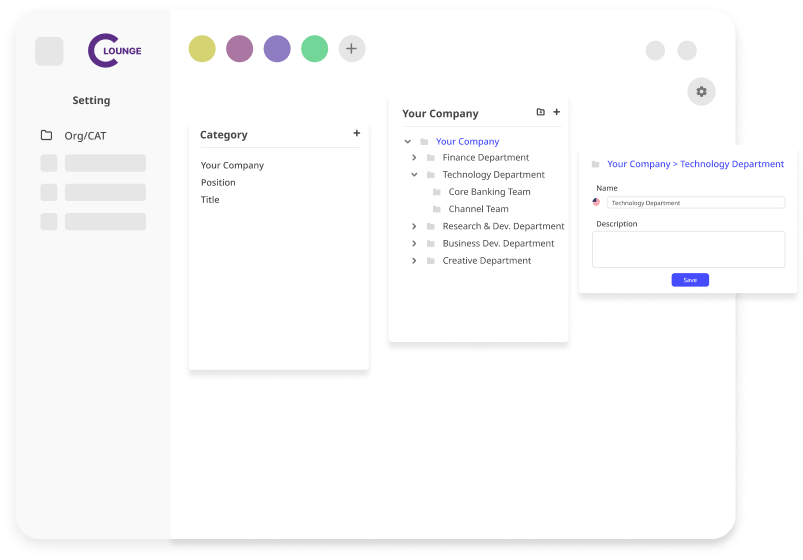
Business Classification Management
Integrate and manage categories to be used throughout the system, such as organization charts, positions, and knowledge categories.
Service & Features
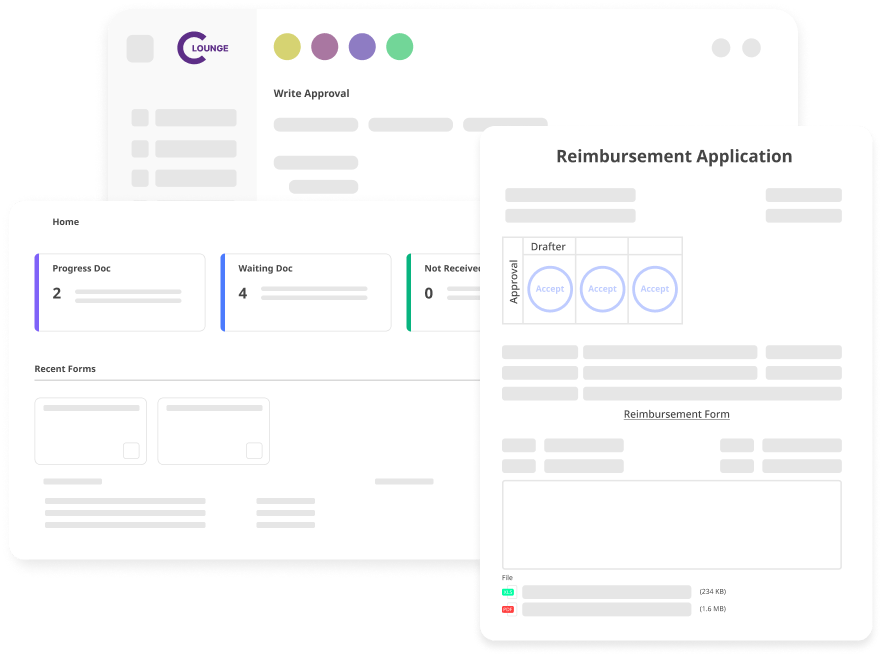
e-Approval
Various electronic approval templates are provided and company-specific approval processes can be applied, enabling efficient and quick work.
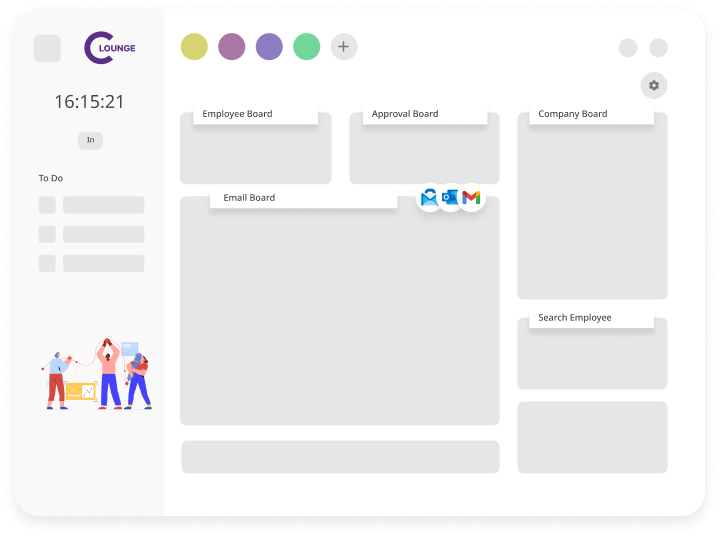
Business Portal
Experience seamless business operations by linking and integrating a range of powerful features all on one page, streamlining your workflow and increase efficiency.
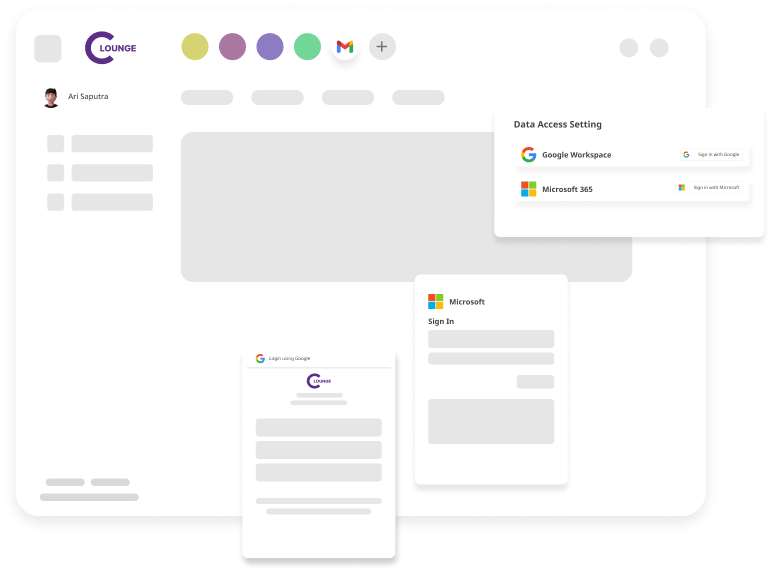
Integrated Workspace
Integrate SaaS services like Google Workspace or Microsoft 365 to customize your workspace by adding apps to the work portal.
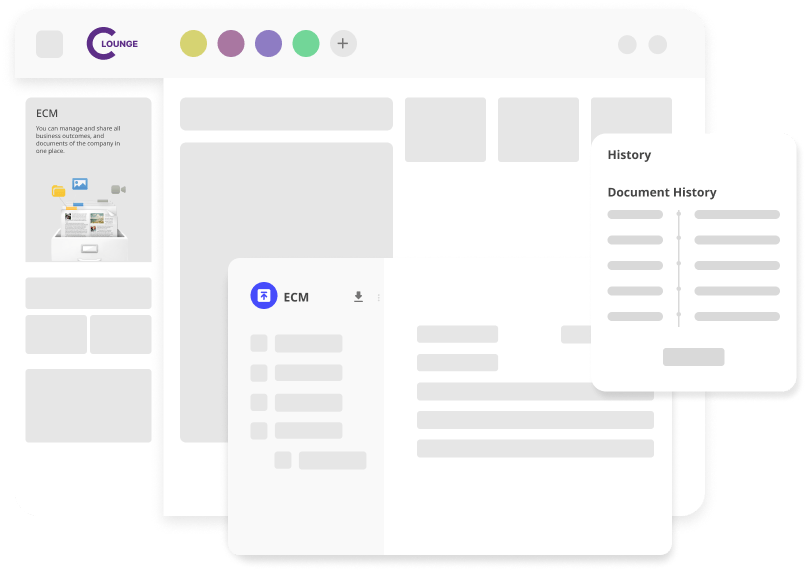
Enterprise Content Management (ECM)
You can effortlessly save documents, streamline workflows, and share files, addressing your needs for efficient document management and collaboration
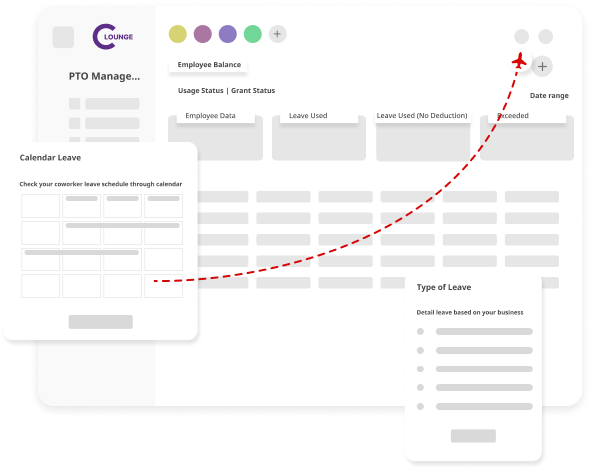
Leave Management
Leave management is the set of practices for managing, requesting, and guiding people leave within your organization.
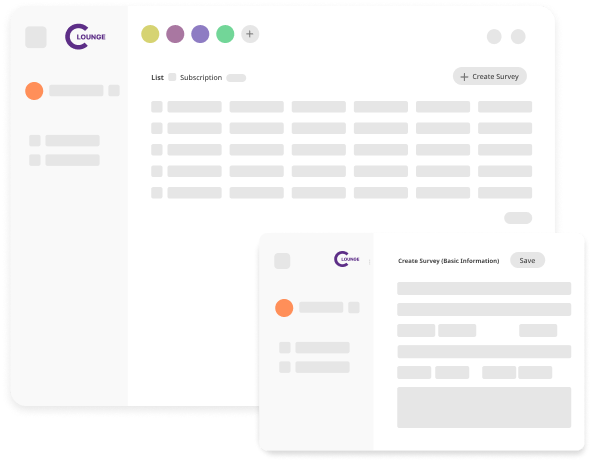
Survey
Design and manage professional surveys with ease — from drafting questions to sharing across channels. Monitor responses in real time, control participation visibility, and generate insights that drive better decisions.
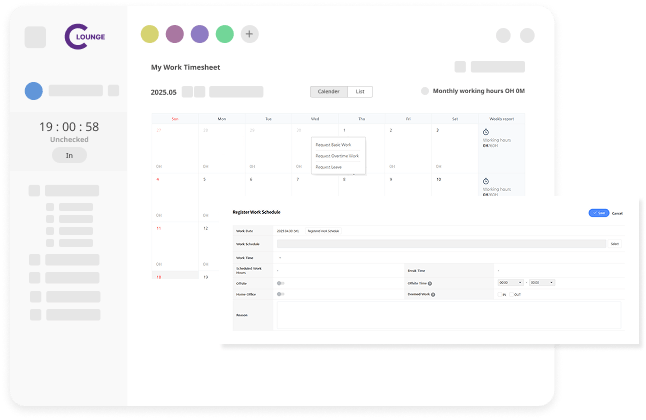
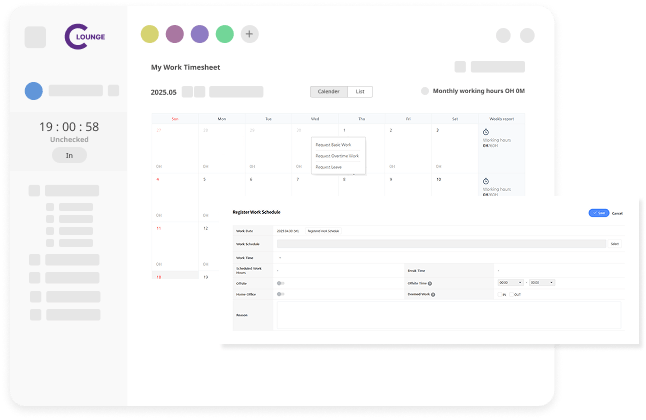
Attendance Management
Track and manage employee attendance effortlessly — from real-time check-ins to comprehensive reporting. Get complete visibility, automate records, and ensure policy compliance with ease.
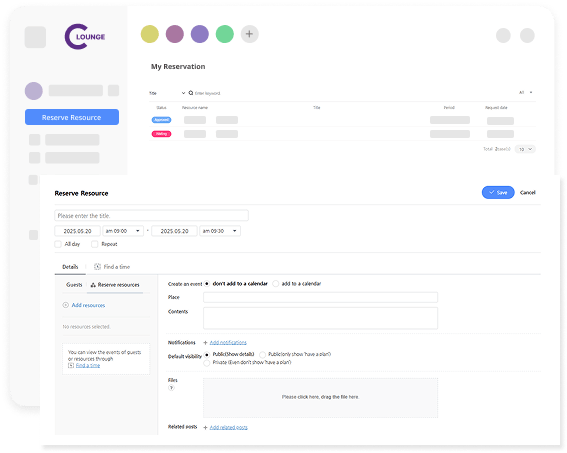
Resource Management
Easily allocate, track, and optimize your organizational resources — from tools and facilities to personnel and project assets — all in one centralized system.
Task Management
Organize, assign, and track tasks with clarity. Stay on top of deadlines, boost team collaboration, and manage workloads effectively — all from a simple, structured workspace.